The enigmatic world of onion links frequently presents a intriguing challenge for explorers. These veiled connections, shrouded in layers of encryption, present unconventional pathways to information that lie hidden from the casual observer. For those seeking hidden insights and willing to delve into the unknown, understanding onion links is crucial.
A thorough exploration of these pathways requires a insightful approach. One must cultivate the ability to traverse through the complexities of onion services while remaining vigilant of potential risks. This guide aims to illuminate the intricacies of onion links, empowering users with the knowledge required to effectively interact into this mysterious realm.
- Before embarking on your journey into the world of onion links, it is essential to acquaint yourself with the inherent risks involved.
- Always confirm the legitimacy of any onion service you encounter.
- Implement robust security measures, such as a reputable VPN and strong passwords, to safeguard your privacy and well-being.
Delving into the Hidden Web: Deciphering Onion Link Addresses
The obscured web, often known as as "the Onion Web," preserves a trove of secrets. Accessing this realm requires interpreting the enigmatic language of Onion link addresses. Unlike traditional URLs, Onion links are composed of multiple layers represented as strings of symbols. These sequences often appear convoluted at first glance, but with a analytical eye, one can start to interpret these cryptic identifiers and unlock the secrets that lie within.
One key component of Onion link addresses is their magnitude. They are typically extensive than conventional URLs, often containing of numerous numbers and letters. Another characteristic feature is the use of the ".onion" domain, which distinctly signifies a website hosted on the Tor network.
- When venturing the hidden web, always practice caution and ensure the authenticity of Onion links before visiting.
- Malware can be hidden within seemingly harmless links, so it is vital to stay vigilant.
Navigating the Labyrinth of Onion Links: A Look at Darknet Security and Privacy
The darknet, a shadowy realm cloaked in anonymity, relies upon onion links as its primary gateway. These encrypted connections, symbolized by .onion domain extensions, guarantee heightened security and privacy for users seeking to circumvent traditional surveillance methods. Despite this, the allure of the darknet comes with inherent risks. Malicious actors often exploit its anonymity to carry out illegal activities, making it a treacherous landscape for the unwary.
Understanding the intricacies of onion links is crucial for either users venturing into the darknet and security professionals striving to track its operations. This requires a deep dive into the cryptographic protocols that power these connections, as well as an awareness of the diverse threats lurking within.
- Training users about best practices for navigating the darknet is paramount to mitigating risks.
- Designing robust security measures and tools that can effectively identify malicious activity within this environment is essential.
Unmasking the Hidden Web: How Onion Links Unlock Forbidden Platforms
Diving into the enigmatic realm of the dark web, one encounters a labyrinthine world shrouded in secrecy. Within this digital underworld, Tor links serve as the primary passage to censored content. These unique addresses, formed using layered encryption, provide access to an array of websites and services existing beyond the reach of government and corporate oversight.
Supporters argue that Onion Links offer a safe haven, allowing individuals to share sensitive information without fear of reprisal. However, the very nature of this hidden world attracts both noble and nefarious elements.
Navigating the Onion Links landscape requires awareness, as the absence of onionlinks regulation can lead to dangerous and deceptive activities. Users must exercise due diligence to avoid falling victim to the potential dangers that lurk within.
This Evolving Landscape of Onion Links: New Challenges and Opportunities
The world of onion links presents undergone a significant transformation in recent times. Once a sanctuary for privacy-conscious users, these masked networks now face complex challenges. Heightened scrutiny from law enforcement agencies and the emergence of new security threats have put pressure on onion link providers to adapt. Simultaneously, this evolving landscape brings exciting opportunities. The creation of novel technologies and protocols promises the potential to enhance security, strengthen anonymity, and promote a more private online experience.
- {For example|Consider,
- decentralized onion link networks could mitigate the risk of single points of failure.
- ,Additionally, moreover,
- blockchain technologies have the potential to
- secure onion link communications, making them extraordinarily more resistant to interference.
The future of onion links lies uncertain. However, it is clear that this compelling technology will continue to play a vital role in the evolving digital landscape.
Peering Beneath the Surface: Exploring the World Accessible Through Onion Links
The cyber realm is a vast and mysterious place, full of hidden nooks. Beneath the surface of everyday websites, there exists a alternative network known as the Dark Web. Accessed through special applications, Onion Links lead you to sites that are anonymous. While this world can be treacherous, it also offers opportunities for exploration that are unavailable in the mainstream.
- Explore the perspectives of people who choose to remain anonymous
- Gain entry to knowledge that is hidden from the general public
- Engage in groups dedicated to a wide range of topics
Nevertheless, caution is crucial because, the Dark Web can also be a risky place. Criminals may operate within this realm, and users should always protect themselves.
 Jonathan Lipnicki Then & Now!
Jonathan Lipnicki Then & Now!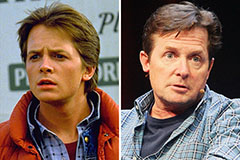 Michael J. Fox Then & Now!
Michael J. Fox Then & Now!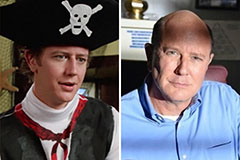 Judge Reinhold Then & Now!
Judge Reinhold Then & Now! Gia Lopez Then & Now!
Gia Lopez Then & Now! Brooke Shields Then & Now!
Brooke Shields Then & Now!